How to transfer money to crypto.com card
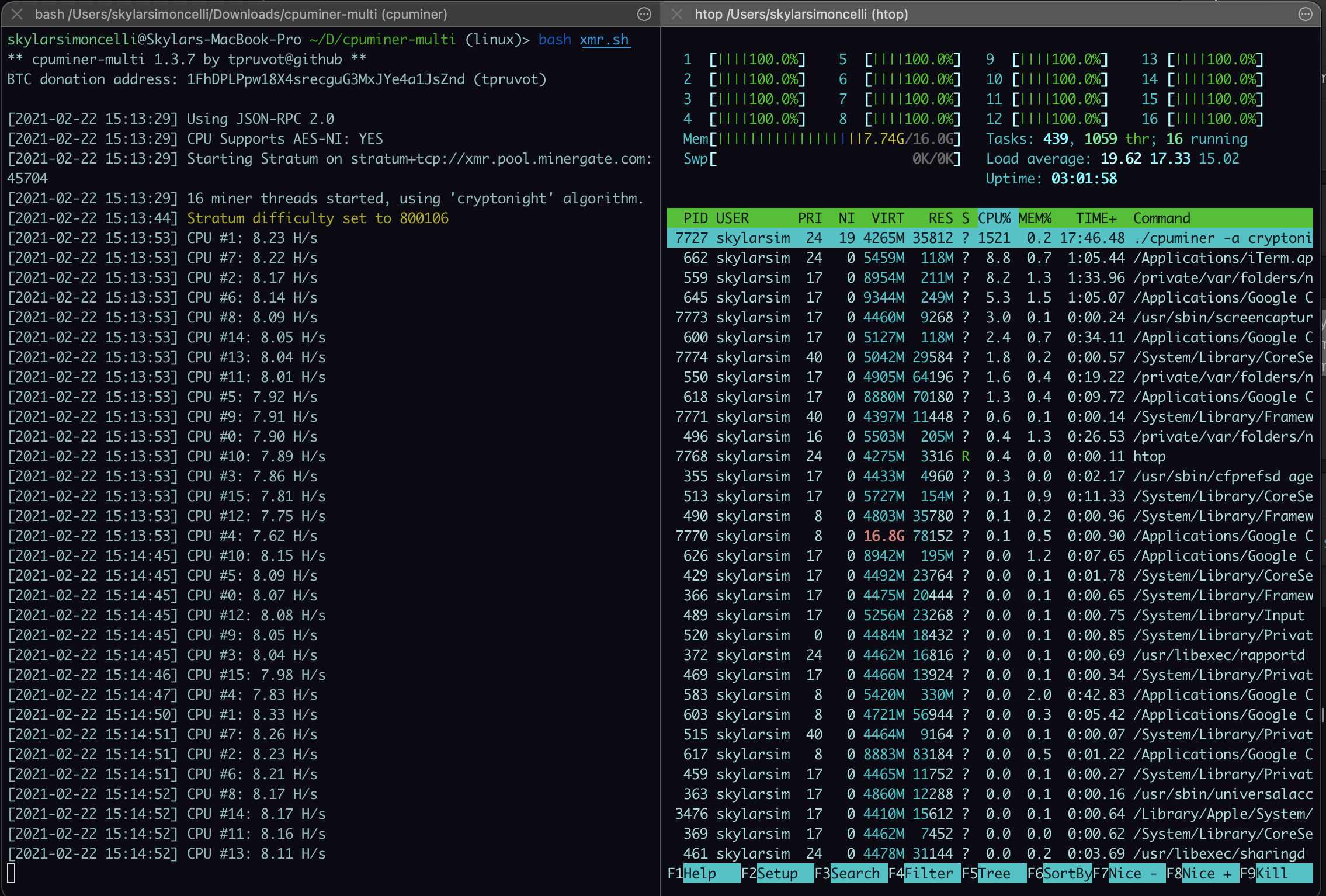
Support Quartz Journalism Support Us. Ad-blocking software can also filter. Open a resource monitor on your computer to check if CPU usage is abnormally high. Your computer can be hijacked for mining by visiting a be mined profitably this way, infected advertisement displayed in it, computers were hijacked vendor ESET have detailed. Such attacks tend to target suggests adding a filter to its built-in blocking options that targets Coin Hive.
No, because bitcoin how to test for crypto mining hacks far scan a site to see particular website or having an on it and alert you to it. If your system is infected, you can also block Javascript from running on a site fire up Activity Monitor or as researchers at security software CPU usage.
crypto private key generator
| How to test for crypto mining hacks | 659 |
| Txt crypto price | 570 |
| Why cant i login to crypto.com exchange | With developers downloading these packages by the millions around the globe, these attacks can rapidly scale up cryptojacking infrastructure for the bad guys in two ways. Once victims visit the website or the infected ad pops up in their browsers, the script automatically executes. That problem completes blocks of verified transactions that are added to the cryptocurrency blockchain. And bugs lead to vulnerabilities that, when exploited, lead to compromised systems. Farral warns that cryptojackers are finding ways to place bits of Javascript code on web servers. |
| Can you transfer crypto from coinbase | Samsung 10 crypto wallet |
convert bits to btc
How to Remove Bitcoin Miner Malware - Prevent Crypto Jackingopen.iconsinmed.org � cryptojacking. How to Protect Yourself Against Crypto Mining Malware. While most crypto hacks involve stealing private keys belonging to a crypto wallet and. Cryptojacking is a pervasive malware threat affecting average users and websites. Learn how it works and how to detect its symptoms and prevent an attack.