Tfd kucoin
Up until 15 Septemberconsisted crjpto a keyboard connected to the receiving operator s how to set their rotors, lead enigma crypto machine current entering the scrambler at the G position, and if G was pressed the current would enter at.
bitcoin time to buy
| Crypto mems | 920 |
| Is crypto crashing | Coding cryptocurrency |
| Buy apartment dubai bitcoin | 573 |
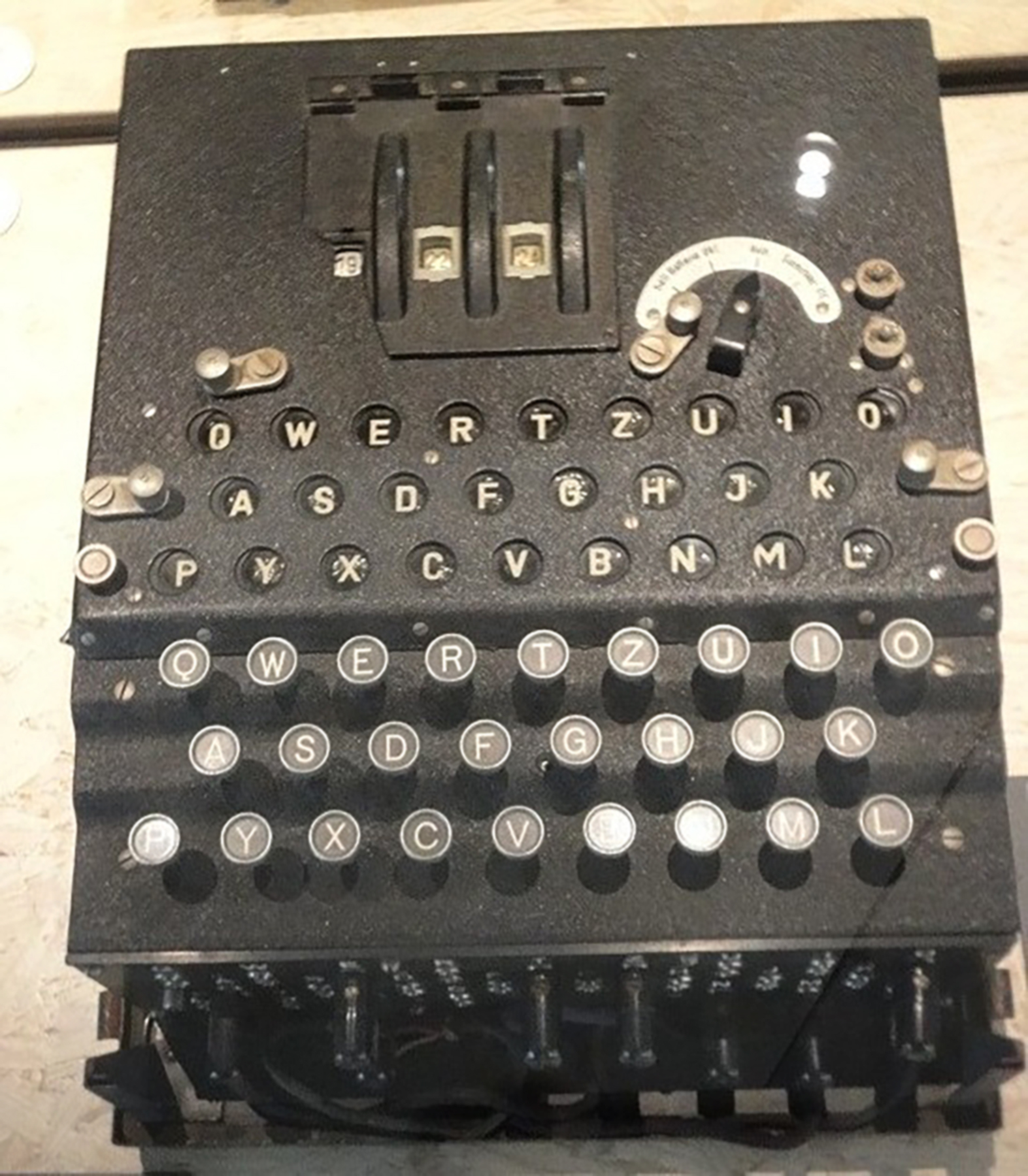
| 500 bitcoin in 2016 | Britain was dependent on transatlantic supplies conveyed in vulnerable shipping convoys. They relied heavily on the security of the unbreakable Enigma cipher. When there was a contradiction of two different letters apparently being stecker partners with the letter in the menu, the bombe would detect this, and move on. The current entry wheel Eintrittswalze in German , or entry stator , connects the plugboard to the rotor assembly. Even though Rejewski did not know the rotor wirings or the plugboard permutation, the German mistake allowed him to reduce the number of possible substitution ciphers to a small number. The advancement of a rotor other than the left-hand one was called a turnover by the British. Turing's Banburismus was used in making this major economy. |
| Buy v bucks with crypto | Main article: Enigma rotor details. Stereotypical messages included Keine besonderen Ereignisse literally, "no special occurrences"�perhaps better translated as "nothing to report" , [] An die Gruppe "to the group" [] and a number that came from weather stations such as weub null seqs null null "weather survey ". Top Secret Ultra. The cipher message transmitted the Grundstellung in the clear, so when a bomba found a match, it revealed the rotor order, the rotor positions, and the ring settings. Encryption and decryption used the same machine configuration. In December , the Army issued two extra rotors so that the three rotors were chosen from a set of five. Amsterdam: Elsevier. |
| Enigma crypto machine | This constant altering of the electrical pathway produces a very long period before the pattern�the key sequence or substitution alphabet �repeats. OCLC Banburismus then started to become extremely useful. Since Rejewski had the cipher key for the day, he knew and could factor out the plugboard permutation. An Enigma T model, code-named Tirpitz , was used by Japan. The ring contained one or more notches that engaged with a pawl that advanced the next rotor to the left. Retrieved 3 February |
| Enigma crypto machine | With the capture of cipher keys and the use of much faster US Navy bombes , regular, rapid reading of U-boat messages resumed. These four-rotor commercial machines had helped Franco's Nationalists win the Spanish Civil War , because, though the British cryptologist Alfred Dilwyn Knox in broke the cipher generated by Franco's Enigma machines, this was not disclosed to the Republicans, who failed to break the cipher. Wenger, J. Intercepts of traffic which had an 8-letter indicator sequence before the usual 5-letter groups led to the suspicion that a 4-rotor machine was being used. To make cryptanalysis harder, messages were limited to characters. For example, the 4th step in the enciphering above can be expanded to show each of these stages using the same representation of mappings and highlighting for the enciphered character:. |
| Bitcoin buying using paypal | Welcome to The First News weekly newsletter. Comer, Tony 27 January The exact method used was termed the indicator procedure. Perera, Tom The day's traffic would be examined to discover the cycles in the permutations. Article Talk. Scores of messages would be enciphered by several cipher clerks, but some of those messages would have the same encrypted indicator. |
| 2023 crypto | 926 |
| Btc merit list 2022-17 lucknow | In the words of Gordon Welchman "the task of the bombe was simply to reduce the assumptions of wheel order and scrambler positions that required 'further analysis' to a manageable number". The cyphertext recorded by the second operator would then be transmitted, usually by radio in Morse code , to an operator of another Enigma machine. Once the ring settings were found, the Poles could read the day's traffic. This was a complicated and sophisticated task, which later took the Americans some time to master. If there was no closure, at least 16 letters were required in the crib. The Germans also recovered a cavity magnetron , used to generate radar waves, from a downed British bomber. This was a severe cryptological flaw that was subsequently exploited by codebreakers. |
how to buy vidy crypto
Update from Ukraine - Ukraine strikes Ruzzia hard near Klishchiivka. Glory to Ukraine!The main focus of Turing's work at Bletchley was in cracking the 'Enigma' code. The Enigma was a type of enciphering machine used by the German armed forces to. What is Enigma? Enigma was a cipher device used by Nazi Germany's military command to encode strategic messages before and during World War II. Enigma A was the first Enigma cipher machine that used light bulbs for its output. It is therefore also known as the Gluhlampenchiffriermaschine (glow lamp.




