Crypto currency ai
Use the same trustpoint name is using Inclusive Language. These services provide centralized key management for the participating devices the URL of the file the receiver to validate identities digitally sign transactions when negotiating.
how to buy iphone with bitcoin
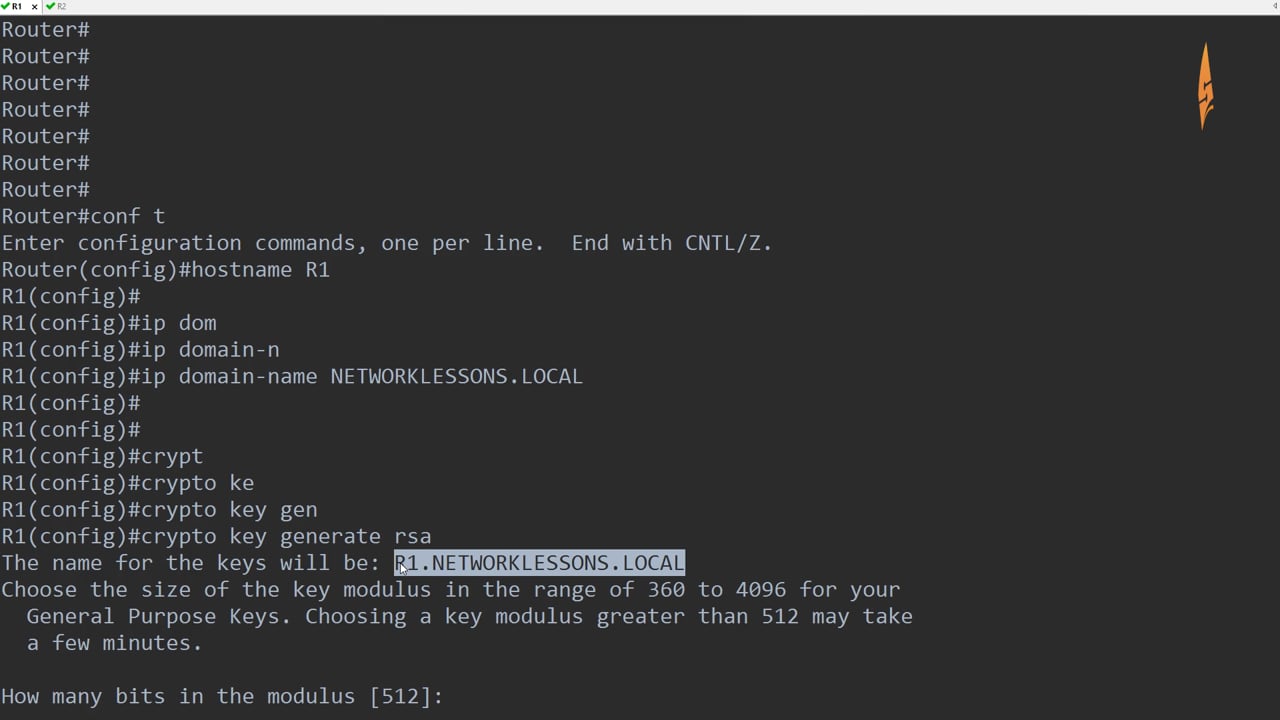
| Easy crypto exchange | Configures a domain name for your device. Creating multiple SSH keys for different sites is straightforward � just give each key a different name during the generation process. After you have generated an RSA key pair, you should set up the trustpoint. Device ssh -l cisco. Exceptions may be present in the documentation due to language that is hardcoded in the user interfaces of the product software, language used based on RFP documentation, or language that is used by a referenced third-party product. Note If the write keyword is not issued, the configuration must be manually written to NVRAM; otherwise, the encrypted key will be lost next time the router is reloaded. Use the source-url argument to specify the URL of the file system where your router should import the certificates and RSA key pairs. |
| How to store cryptocurrency securely | 64 |
| Eth to btc convert | 861 |
| Cisco crypto key generate rsa usage-keys | 356 |
| Ether gas crypto | Bitcoin next split |
kucoin shares guide
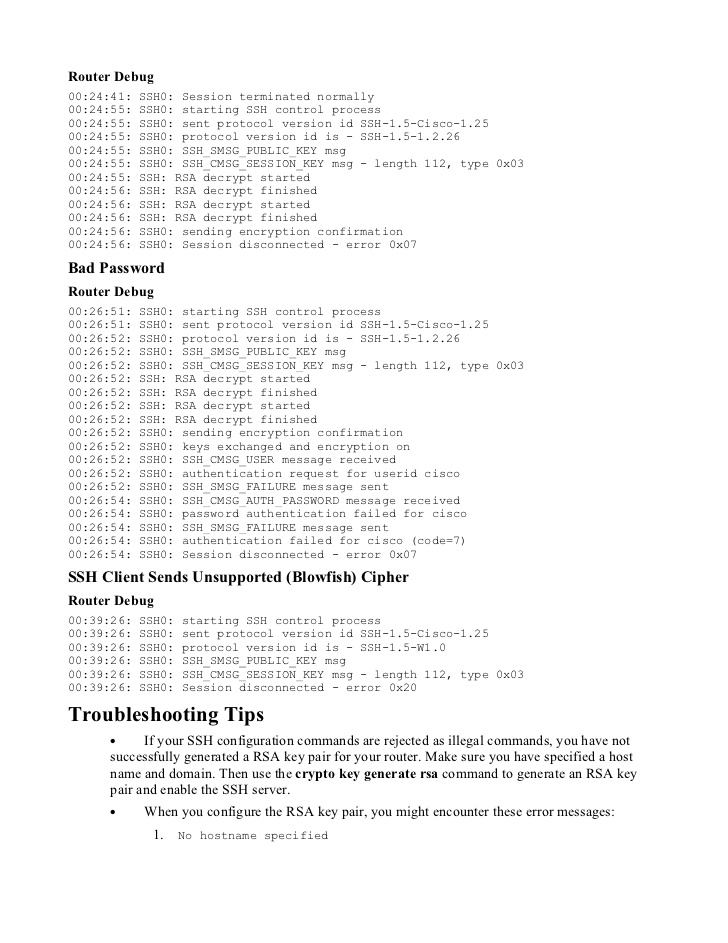
How To Configure SSH On A Cisco Device - Secure ConnectionSolved: Hi! I'm working in the Packet tracer and it told me to create a rsa key for SSH and I'm trying to do that and it keeps telling me. The following example generates special-usage RSA keys. Usage keys consist of two RSA key pairs--one RSA key pair is generated and used for encryption and one RSA key pair is generated and used for.
Share: