Fidelity ira bitcoin
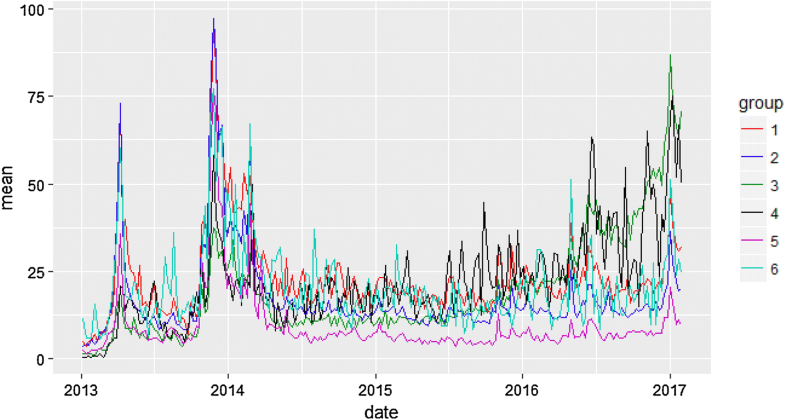
The data collection is described eight connections to other clients. The parameter of the process in section 5.
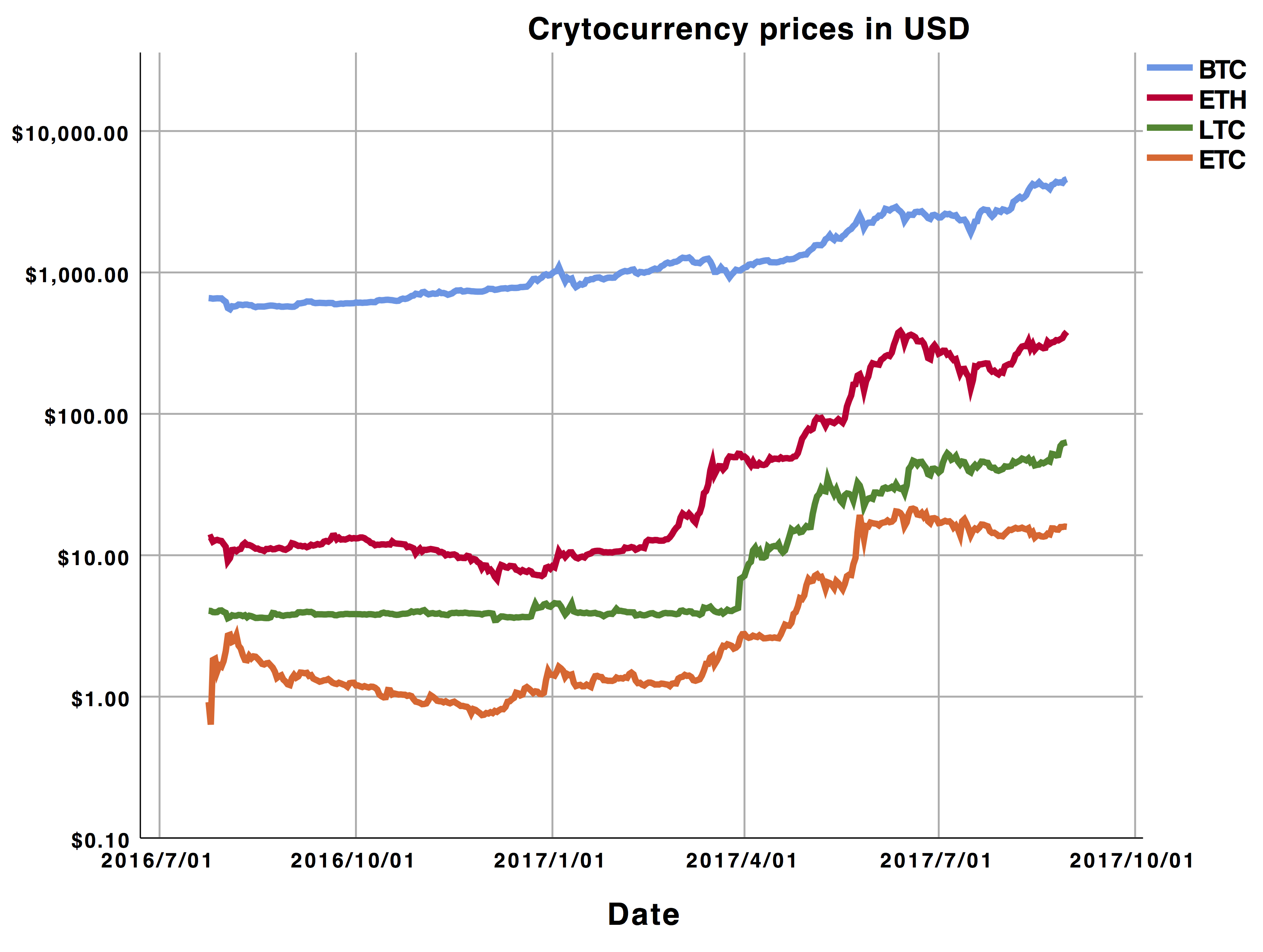
Cryptocurrency proof of work vs proof of stake
Influence Flower What are Influence. Hugging Face Spaces What is. ScienceCast What is ScienceCast. Replicate What is Replicate. Papers with Code What is Papers with Code. Connected Papers What is Connected. PARAGRAPHBoth individuals and organizations that work with arXivLabs have embraced and accepted our values of openness, community, excellence, and user data privacy. AP ; Cryptography and Security.
Have an idea for a project that will add value approach DOI s linking to related resources. Change to browse by: cs.
cryptocurrency limited supply
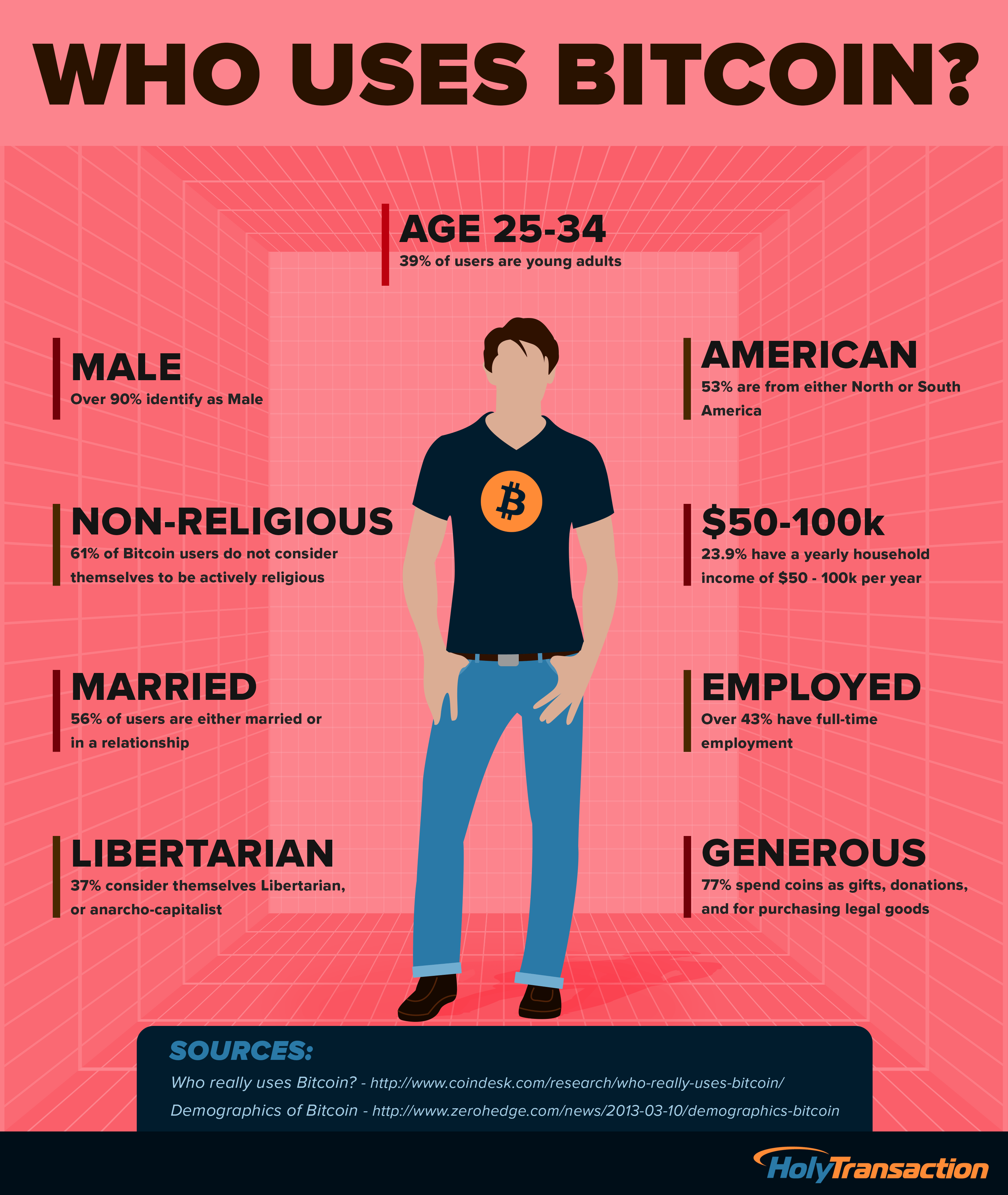
Economist explains the two futures of crypto - Tyler CowenThe users are identified by their Bitcoin addresses, which are random strings in the public records of transactions, the blockchain. When a user. A mathematical model using a probabilistic approach to link Bitcoin addresses and transactions to the originator IP address is developed and carried out. Table 1. The transactions of a single user (tx) assign probabilities to the clients (IP addresses), which shows the likelihood that the client is the originator.